Mobile Access is gaining popularity for employee credentials. As work environments become mobile-friendly, transitioning to mobile credentials is the next step for organizations.
There have been numerous approaches to enabling mobile access control, such as microSDs, add-on sleeves, MIFARE Classic, NFC Peer-to-Peer, and Bluetooth Classic. Historically, these technologies have their own set of challenges and have been adapted to create more effective mobile access technologies.
What are the current technologies that support mobile access?
1) Near Field Communication (NFC)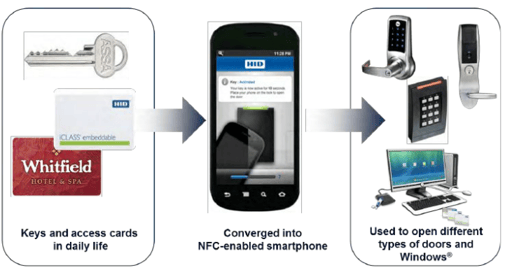 Until recently, the only way to enable mobile credentials on a mobile phone was by creating a Secure Element, such as a Sim Card. In 2014, Google released a new NFC feature called Host-Based Card Emulation. Rather than having a secure element, the new NFC feature allows the contactless card to be hosted in an app. Now, it is possible to use standard-based card technology with NFC readers to use mobile credentials.
Until recently, the only way to enable mobile credentials on a mobile phone was by creating a Secure Element, such as a Sim Card. In 2014, Google released a new NFC feature called Host-Based Card Emulation. Rather than having a secure element, the new NFC feature allows the contactless card to be hosted in an app. Now, it is possible to use standard-based card technology with NFC readers to use mobile credentials.
Cons with this technology: Currently, this technology is not supported by iPhone.
2) Bluetooth Smart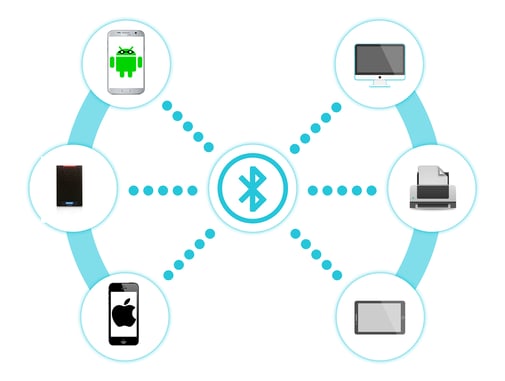 Bluetooth Smart is the best option available for mobile credentials. Bluetooth Smart is supported on both Android and Bluetooth systems. Additionally, Bluetooth smart has a low power consumption, there is no pairing needed, and can support long-range distances. This will allow you to place the readers in a safe location or hidden location.
Bluetooth Smart is the best option available for mobile credentials. Bluetooth Smart is supported on both Android and Bluetooth systems. Additionally, Bluetooth smart has a low power consumption, there is no pairing needed, and can support long-range distances. This will allow you to place the readers in a safe location or hidden location.
Conclusion
Managing employee credentials is a time-consuming process that can take up valuable time and resources. The development of technologies supporting mobile credentials touches on a pain point the security industry faces daily. Rather than ordering and printing ID cards, managing mobile credentials allows your employees to virtually receive their credentials. The employee simply has to open up an app to receive their credentials instead of spending time going to get their physical badge. As these technologies develop, mobile credentials will become the norm.
Watch the video below to learn more about mobile credentials:
Would you like more information? Click below:







